Table of Content
- Introduction
- Benefits of Incorporating MITRE ATT&CK in SIEM
- Best Practices to Successfully Integrate MITRE ATT&CK in SIEM
- Conclusion
Introduction
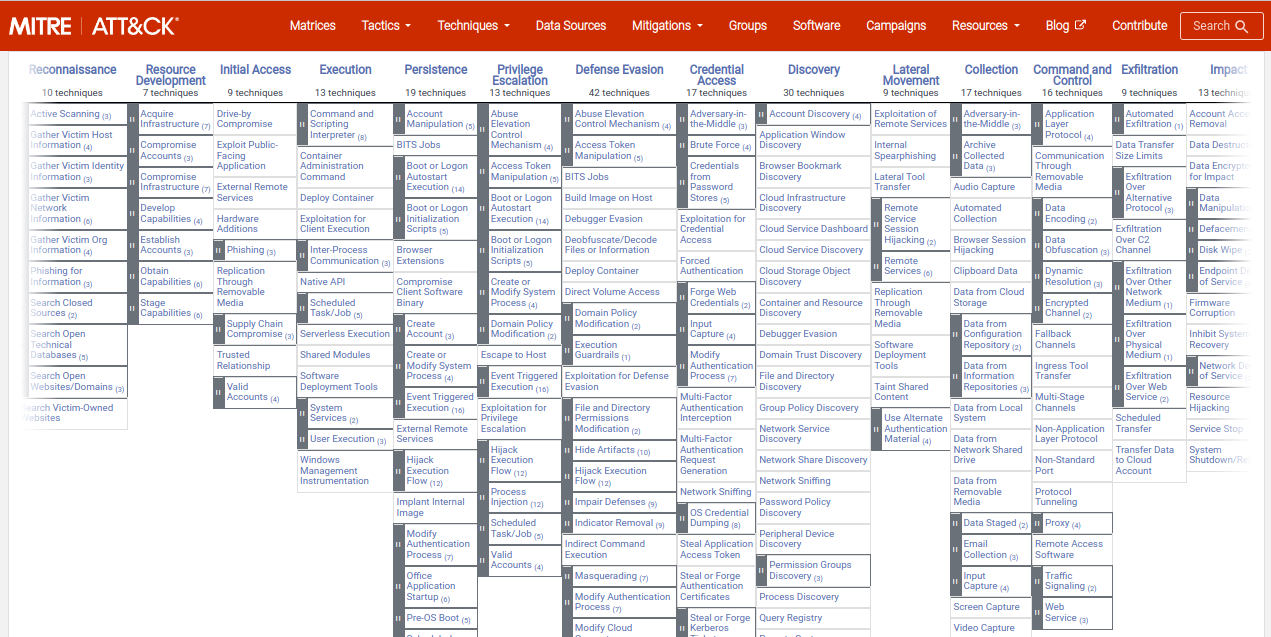
MITRE ATT&CK is a widely-used framework for understanding and defending cyber attacks. Developed by the MITRE Corporation, the ATT&CK framework provides a comprehensive taxonomy of attack tactics and techniques that can be used to improve an organization's security posture. One way to incorporate MITRE ATT&CK into your organization's security strategy is through the use of a SIEM (Security Information and Event Management) system.
SIEM systems are designed to collect, analyze, and alert on security-related data from a variety of sources, including network traffic, endpoint logs, and system events. By integrating MITRE ATT&CK into your SIEM system, you can improve your ability to detect and respond to cyber attacks. Explaining this in detail, let us see how incorporating MITRE ATT&CK in SIEM can benefit your organization. Further, we have also shared some best practices for successful integration of MITRE ATT&CK in SIEM.
Benefits of Incorporating MITRE ATT&CK in SIEM
Incorporating MITRE ATT&CK in SIEM Strategy shouldn't really be a second thought for those looking to strengthen their cybersecurity posture. Explaining the significance in detail, here are some key benefits of incorporating MITRE ATT&CK into your SIEM strategy:
1. Improved Threat Detection:
MITRE ATT&CK provides a comprehensive framework for understanding the tactics and techniques used by attackers. By incorporating this framework into your SIEM system, you can improve your ability to detect and alert suspicious activity. This can help you identify attacks at an earlier stage in the cyber-attack life-cycle and thereby reduce the impact on your organization.
2. Enhanced Threat Response:
MITRE ATT&CK also provides detailed information on the tactics and techniques used by attackers, as well as potential countermeasures to mitigate or prevent such attacks . By incorporating this information into your SIEM system, you can improve your ability to respond to attacks. This can help you mitigate the attack and reduce the impact of an attack and also the likelihood of any such similar attacks in future.
3. Enhanced Compliance:
Many compliance frameworks, such as PCI DSS and NIST 800-53, require organizations to have a robust security posture. By incorporating MITRE ATT&CK into your SIEM strategy, you can demonstrate that you are taking a proactive approach to security. This can help you meet compliance requirements and avoid costly fines.
Read: Benefits of Integrating MITRE ATT&CK with SIEM
Best Practices to Successfully Integrate MITRE ATT&CK in SIEM
1. Understand Business Security Objectives
Every business has a different take on cybersecurity and has different goals and objectives for establishing a robust security program. While the core objective remains to be the same, yet in most cases the security goals are greatly influenced and defined by the industry standards, regulations and mandates that the organizations are expected to meet. So, taking into consideration the business security objectives, setting up and integrating the MITRE ATT&CK with the SIEM systems, while in alignment with the security goals is crucial. This will ensure successful integration and accurate detection and reporting of threats in the environment.
2. Understand MITRE ATT&CK Framework
If your organization plans to leverage the MITRE ATT&CK framework, then integrating it with the SIEM system is the best way to do so. For organizations to successfully integrate ATT&CK with SIEM, understanding the framework is the key. By successful integration we mean ensuring appropriate functioning of the SIEM systems to provide accurate security intelligence and alerts. Learning and understanding the framework provides an in-depth perspective and insight into the various stages of the cyber-attack life cycle. Further, understanding the MITRE framework helps in mapping the defined use cases with the SIEM rules which is critical for accurate detection, alert and response to threats.
3. Map SIEM Use Case with MITRE ATT&CK Framework
The MITRE ATT&CK framework is very important from a cybersecurity risk detection and risk analysis perspective. It is an invaluable tool for the cybersecurity professionals as it offers a vast knowledge base on various threat information. This would be in terms of information on various techniques, tactics and procedures used by various threat actors. Having such insightful cyber threat intelligence at your fingertips is essential for an organization to build a strong defense against the evolving threats. So, mapping the extensive use cases defined in the ATT&CK framework with the SIEM rule is an essential step in the MITRE ATT&CK & SIEM integration process. Mapping with MITRE ATT&CK’s vast library of use cases, helps identify and address the security gaps in the existing system and further facilitates reduced detection gaps and delayed automated response to threats.
4. Conduct Risk Assessment & Prioritize Risk
Risk or threat response are often set and generated based on the high-risk high-priority classification. So, for organizations to ensure that the alerts generated are accurate and with the least number of false positives, conducting a thorough risk assessment and classifying the risk as low, medium or high priority is essential. This is important for receiving accurate intelligence reporting, threat detection, and alert generation. This will help the SOC team stay ahead in their operations of detecting, analyzing, responding and addressing various threats the IT Infrastructure is exposed to.
5. Testing & Reviewing of MITRE & SIEM Integration
Testing and reviewing is a very critical phase in the integration process for the IT team. This is to simply test and ensure that the integration process is a success and the systems are functioning right. The security systems and processes must be put to test in order to gauge the effectiveness of system functionality in terms of the existing defense, threat detection capabilities and automation of response and alert generation for attacks by various adversaries.
6. Training the SOC Team
Integrating the MITRE ATT&CK in SIEM can be a daunting task for the SOC team. For the organization to ensure successful integration, it is essential that the team involved and handling the entire process are well trained and proficient with the systems. So, conducting regular training programs for the team is essential in this journey. The training program will not just help the team familiarize and learn about the real-world adversary tactics, techniques, and procedures (TTPs), but also help them understand ways of applying the ATT&CK to further improve the threat intelligence practices.
7. On-going Evaluation & Updation of SIEM System
Incorporating MITRE ATT&CK into your SIEM strategy is not a one-time task. It requires ongoing effort to ensure that your SIEM system is up-to-date with the latest information from the ATT&CK framework. This can include regularly updating your SIEM system with new attack tactics and techniques, as well as reviewing and updating your detection and response rules.
It is also important to note and understand that to successfully incorporate MITRE ATT&CK into your SIEM strategy, it is also essential to have the right tools and expertise.
Read : Steps to Develop custom rules and alerts based on MITRE ATT&CK techniques and tactics
Many SIEM vendors offer solutions that are specifically designed to integrate with the ATT&CK framework. These solutions can help you quickly and easily incorporate MITRE ATT&CK into your SIEM system.
Conclusion
In conclusion, incorporating MITRE ATT&CK into your organization's SIEM strategy can provide numerous benefits. This includes improved threat detection, quick and effective threat response, and enhanced compliance with various industry relevant security standards and regulatory mandates. By taking proactive measures and approach to security, you can protect your organization from cyber attacks and reduce the impact of any attack that occurs in the environment.
DNIF HYPERCLOUD is a cloud native SIEM that provides single click security coverage overview based on the MITRE ATT&CK framework. This has helped several organizations strengthen their security posture through a systematic, phased approach. Book a demo to know how DNIF HYPERCLOUD's innovative architecture can bolster your security capabilities.

